
Redefining hosting solutions for AI
In recent years, the data centre market has witnessed a remarkable surge in energy consumption, largely attributed to the escalating demands of artificial intelligence (AI). This trend, as highlighted...

In recent years, the data centre market has witnessed a remarkable surge in energy consumption, largely attributed to the escalating demands of artificial intelligence (AI). This trend, as highlighted...

We understand that moving data centre can be a very scary transition to make. You need to know you’re in safe hands and that you can put your trust in a provider who has the skills and...

As the transition from VMware to Broadcom looms, it's imperative for organisations to understand the timeline and take the necessary actions promptly.

In November 2023, the cloud computing technology provider, VMware, was acquired by the global software provider, Broadcom, in a move to build out its multi-cloud strategy. The $69bn acquisition...
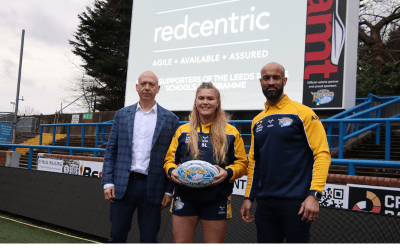
Redcentric is proud to announce its partnership with the iconic Leeds Rhinos for the 2024 Super League season. The collaboration aims to provide an unforgettable experience for 3,000 adults and...

Thackray Museum has had a technological boost provided by Redcentric which will undoubtedly play a crucial role in shaping its success.

We are pleased to announce that Redcentric will be attending Fortinet's Security Day on 18th April.