
Improving Customer Experience with Voice
Omni-channel communication is a game-changer in handling increasing customer expectations and an increasing number of customer touchpoints.

Omni-channel communication is a game-changer in handling increasing customer expectations and an increasing number of customer touchpoints.

Are you tired of the tedious process of recording messages for your phone system? We look at how our bespoke text-to-speech application can transform your telephony experience.

In today’s fast-paced business landscape, enterprises are constantly challenged by a myriad of obstacles, ranging from operational inefficiencies to intricate decision-making processes....

In November 2023, the cloud computing technology provider, VMware, was acquired by the global software provider, Broadcom, in a move to build out its multi-cloud strategy. The $69bn acquisition...
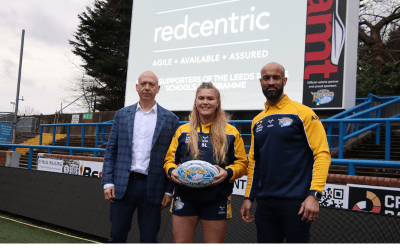
Redcentric is proud to announce its partnership with the iconic Leeds Rhinos for the 2024 Super League season. The collaboration aims to provide an unforgettable experience for 3,000 adults and...

Thackray Museum has had a technological boost provided by Redcentric which will undoubtedly play a crucial role in shaping its success.